Zero trust is gaining popularity among security leaders, with a large majority of organizations already implementing or planning to adopt this strategy.
According to the HashiCorp State of Cloud Strategy Survey, a significant 89% of participants emphasized the importance of security for successful cloud implementation. However, as organizations embrace the cloud, they face the challenge of reevaluating their approach to securing applications and infrastructure. The traditional notion of security, defined by a static and IP-based perimeter, is evolving into a dynamic and identity-based paradigm with no clear boundaries. This transformative concept is commonly referred to as zero trust security.
The increasing adoption of zero trust reflects the rising security challenges faced by enterprises. Organizations have seen their attack surfaces expand as remote work policies become more prevalent and endpoint devices are used outside the corporate network. Concurrently, the frequency and intensity of cyberattacks have significantly increased.
Zero Trust is based on three guiding principles that shape its implementation:
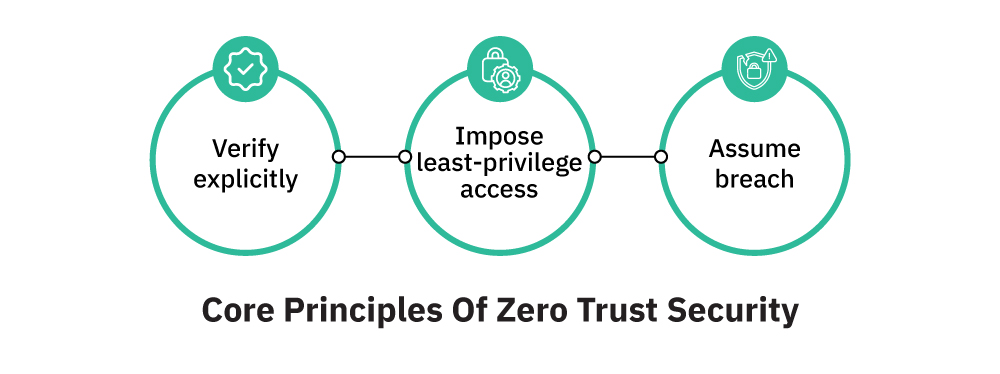
Verify explicitly: The Zero Trust paradigm does not assume trust by default. Users must actively request access to resources, and they must provide proof of identification. Authentication and authorization are required depending on a variety of data points, such as user identification, location, device, service or workload, data classification, and anomalies.
Impose least-privileged access: Each user is only given the privileges required for their work. This restricts users to just-in-time and just-enough access, employs risk-based adaptive controls, and implements data security measures. As a result, the risk of unintentional or purposeful misappropriation of corporate assets is reduced.
Assume breach: Until proven otherwise, every user within the organization, including employees, contractors, partners, and suppliers, is regarded as potentially malicious. To guard against this risk, security measures should be put in place. Access must be segmented by network, user, device, and application, and data must be encrypted. Analytics must be used for threat detection and better security.
Top use cases of Zero Trust
Reducing business and organizational risk: Zero-trust solutions ensure that applications and services can communicate only after verification based on their identity attributes. This approach reduces risk by uncovering the presence of assets on the network and how they communicate. Moreover, zero-trust strategies eliminate overprovisioned software and services while continuously verifying the credentials of every communicating asset.
Gaining access control over cloud and container environments: The migration to the cloud raises concerns regarding access management and loss of visibility. Zero-trust architecture addresses these concerns by applying security policies based on workload identities directly tied to the workloads themselves. This approach ensures that security remains closely integrated with protected assets, independent of network constructs like IP addresses or ports, and guarantees consistent protection as the environment evolves.
Thorough inspection and authentication: Zero trust operates on the principle of least privilege, assuming every entity to be hostile. Each request undergoes a thorough inspection, including authentication and permissions assessments for users and devices, before granting trust. Continual reassessment occurs as contextual factors change, such as user location or accessed data. By eliminating trust assumptions, even if an attacker infiltrates the network through a compromised device, their ability to access or steal data is restricted due to the zero-trust model’s secure segment isolation.
4 reasons organizations are opting for Zero Trust security
Enhanced cybersecurity: Zero trust models enable companies to establish more effective cybersecurity practices. This provides reassurance that even in the event of a cyberattack, the data remains secure from malicious actors.
Compliance support: Zero trust models help organizations meet compliance requirements, such as HIPAA regulations. By implementing a zero-trust approach, companies can ensure compliance without worrying about potential issues arising later due to non-compliance.
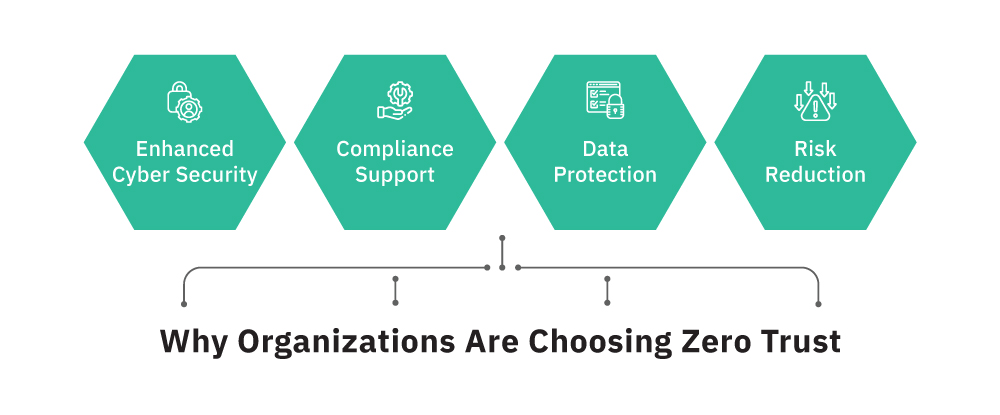
Risk reduction: By allowing access only when needed and limiting unnecessary access, zero-trust models reduce risks for businesses. This approach protects against both internal threats like malware infections and external threats like phishing attacks and ransomware.
Comprehensive data protection: With a zero-trust model, you can have peace of mind knowing that your data is safeguarded. This approach covers a wide range of threats, providing protection against various internal and external risks.
By following the core principles of zero trust, organizations can strengthen their security posture, comply with regulations, reduce risks, and ensure the safety of their valuable data.
Zero trust security with HashiCorp
HashiCorp offers solutions for enterprises that need zero trust security for multi-cloud environments. It manages secrets across multiple clouds and private data centres, enforces security with identity and provides governance through policies. HashiCorp Vault enables enterprises to centrally store, access, and distribute dynamic secrets like tokens, passwords, certificates, and encryption keys across any public or private cloud environment. Unlike burdensome ITIL-based systems, HashiCorp solutions issue credentials to both people and machines in a dynamic fashion, creating a secure, efficient, and multi-cloud solution suited to today’s insecure world.
It’s part of the company’s “zero trust” security which secures everything based on trusted identities. Organizations can use zero trust to manage the transition to the cloud while maintaining the level of security required, one that trusts nothing and authenticates and authorizes everything.
There are now thousands of companies who seek to leverage the cloud (whether hybrid or multi-cloud) to run mission-critical workloads. It’s imperative that they seriously consider zero trust to secure access to authorized personnel. That’s where Cloud Kinetics and HashiCorp can help significantly.
Organizations are rethinking how to secure their apps and infrastructure on the cloud. Security in the cloud is being recast from static, IP-based (defined by a perimeter) to dynamic, identity-based (with no clear perimeter). This is the core of zero trust security.
This is especially true with emerging and booming markets. Sandy Kosasih, Cloud Kinetics Country Director for Indonesia, says, “HashiCorp’s approach to identity-based security and access provides a solid foundation for companies to safely migrate and secure their infrastructure, applications, and data as they move to a multi-cloud world.” Suhail Gulzar, HashiCorp’s Regional Manager of Solutions Engineering for Asia, adds: “Companies use different identity platforms for federated systems of record. Leveraging these trusted identity providers is the principle of identity-based access and security. Our products provide deep integration with the leading identity providers.”
How does zero trust enable human-to-machine access?
“Traditional solutions for safeguarding user access used to require you to distribute and manage SSH keys, VPN credentials, and bastion hosts, which creates risks of credential sprawl and users gaining access to entire networks and systems. Cloud Kinetics deploys HashiCorp’s Boundary solution to secure access to apps and critical systems with fine-grained authorizations that don’t require managing credentials or exposing your entire network. This is an excellent security feature to protect the core network.”
Fitra Alim, Cloud Kinetics Country Technology Officer
As security challenges continue to grow, embracing the zero-trust model becomes increasingly crucial for organizations aiming to safeguard their valuable assets from the ever-evolving threat landscape. If you have any questions about improving your cybersecurity practices with zero trust security, get in touch with us. Cloud Kinetics security specialists will be happy to have a non-obligatory discussion with you.